What Is Cloud Workload Security?

Introduction
Cloud workload security safeguards cloud applications across their lifecycle in dynamic, identity-driven environments. As cloud-native architectures expand the attack surface, traditional security models may fail, making workload-specific, real-time protection essential.
What Are Cloud Workloads?
Built for dynamic, identity-driven environments, cloud workload security protects applications across their full lifecycle, supporting workloads that scale, move, and change beyond the reach of traditional security models.
Types of Cloud Workloads
The four main types of cloud workloads differ in how they run, scale, and interact, and each has unique security implications.
- Virtual Machines (VMs): Cloud-hosted compute resembling servers, governed by identity-based access
- Containers and Kubernetes Workloads: Ephemeral, orchestrated workloads built for scale and portability.
- Serverless Functions: Short-lived, event-driven code tightly coupled to cloud identities.
- Managed Cloud Services: Provider-managed services where identities, APIs, and configuration still pose risk.
Cloud workloads are dynamic execution environments shaped by identity, policy, and runtime behavior, not static servers.
What Is Cloud Workload Security?
Cloud workload security focuses on protecting workloads across their full lifecycle by addressing:
- Workload identities and permissions
- Runtime behavior and execution
- Network exposure and communication paths
- Configuration and posture risk
Unlike traditional endpoint security, cloud workload security doesn’t rely on fixed IPs, persistent hosts, or perimeter controls. Instead, it emphasizes identity awareness, continuous visibility, and runtime enforcement.
Effective workload security ensures workloads:
- Operate with least privilege
- Communicate only with approved services
- Execute expected behavior at runtime
Why Cloud Workload Security Is Critical
Cloud environments introduce conditions that traditional security models were never built to handle.
Ephemeral Workloads and Dynamic Scaling
Workloads may exist for minutes or seconds, so security controls must operate continuously and in real time.
Identity-Driven Access Replacing Perimeters
Compromised permissions can be more damaging than exposed ports. Access in the cloud is governed by identities and roles, not network location.
Increased Risk of Lateral Movement
Overly permissive identities and flat trust relationships may allow attackers to move quickly once a workload is compromised. Without workload-focused controls, organizations may struggle to detect abuse, contain breaches, or understand workload behavior.
Common Security Risks Facing Cloud Workloads
Cloud workloads face a distinct set of security risks because of their dynamic, identity-based nature.
Over-Permissioned Identities and Service Accounts
Workloads are often granted broad permissions for convenience, creating high-value targets for attackers.
Misconfigurations and Exposed Services
Open ports, public endpoints, and insecure defaults remain leading causes of cloud breaches.
Lateral Movement Across Cloud Environments
Attackers exploit trust between workloads to move laterally and escalate privileges.
Runtime Threats and Malicious Execution
Compromised workloads can run unauthorized code, access credentials, or exfiltrate data during runtime.
Cloud Workload Security vs Traditional Security Models
Traditional security tools were built for static environments with clear perimeters. Cloud workloads move beyond those assumptions.
- Assets are ephemeral
- IP addresses change constantly
- Network boundaries are fluid
- Identity is the primary control plane
Cloud workload security shifts protection from where something runs to what it is allowed to do.
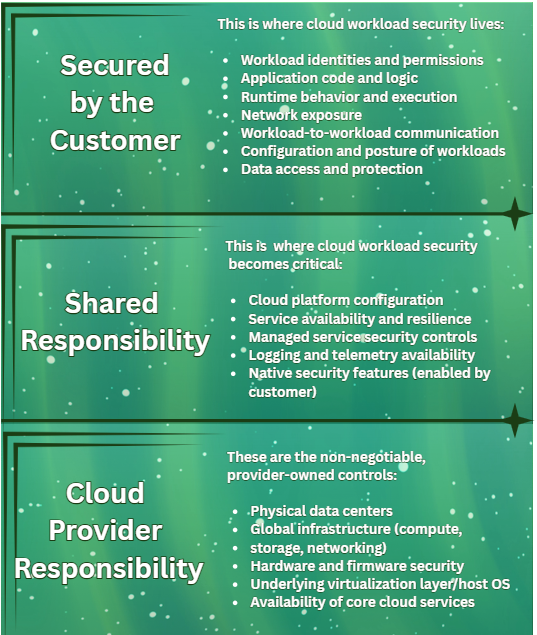
The Shared Responsibility Model in Cloud Workload Security
Cloud security operates under a shared responsibility model, where providers secure the underlying infrastructure while customers retain control of their workloads.
Customers remain responsible for:
- Workload identities and permissions
- Runtime behavior
- Configuration and exposure
- Application logic and data access
Cloud adoption does not transfer security responsibility; it reallocates it.
Core Components of Cloud Workload Security
Cloud workload security is built on a core set of capabilities that protect identities, monitor behavior, and reduce risk across cloud workloads.
Identity and Access Protection
Ensuring workloads operate with least privilege and cannot abuse credentials or roles.
Runtime Threat Detection
Monitoring workload behavior in real time to identify anomalous or malicious activity.
Network Segmentation and Isolation
Restricting workload-to-workload communication to limit lateral movement.
Configuration and Posture Management
Continuously identifying risky configurations and insecure defaults.
Monitoring and Visibility
Providing unified visibility into workload behavior across cloud environments.
Cloud-Native Best Practices for Securing Workloads
Effective cloud workload security aligns with cloud-native principles:
- Enforce least privilege for workload identities
- Continuously monitor execution and access patterns
- Secure workload-to-workload communication by default
- Apply policy-driven controls rather than manual enforcement
Security must be automated, adaptive, and identity-aware to keep pace with cloud environments.
How Cloud Workload Security Fits Into Modern Cloud Security Architectures
Cloud workload security integrates into modern cloud security strategies alongside complementary security platforms such as:
- CNAPP for unified risk visibility
- CSPM for configuration governance
- CWPP for workload-focused protection
It integrates with IAM, DevOps pipelines, and SOC workflows, bringing identity, runtime behavior, and threat response together into a cohesive security model.
Conclusion
Modern cloud security depends on workload-centric protection. Evolving cloud architectures require continuous visibility, identity-based controls, and real-time runtime enforcement for dynamic workloads.
FAQ Section
What is cloud workload security in simple terms?
It protects cloud-based applications by securing their identities, behavior, and configuration throughout their lifecycle.
How is cloud workload security different from endpoint or network security?
It focuses on dynamic workloads and identity-based access rather than static devices or network perimeters.
What types of workloads need cloud workload security?
Virtual machines, containers, serverless functions, and managed cloud services all require protection.
Who is responsible for securing cloud workloads, the cloud provider or the customer?
Cloud providers secure infrastructure; customers secure workloads, identities, and data.
What are the biggest risks to cloud workloads today?
Over-permissioned identities, misconfigurations, lateral movement, and malicious runtime activity.
.gif)
%201.png)